Alert – Phishing Scam Hitting Repossession Community
A new phishing campaign is actively circulating within the repossession industry, and it’s designed specifically to exploit how agents handle complaints, lender communications, and compliance documentation. The message appears legitimate at first glance, presenting itself as a document signature request tied to a repossession-related complaint file. It uses familiar terminology, references a pickup, and includes what looks like an official PDF attachment name tied to complaint handling and lender notification. For many agencies, that combination alone is enough to trigger immediate attention—and that’s exactly what the sender is counting on.
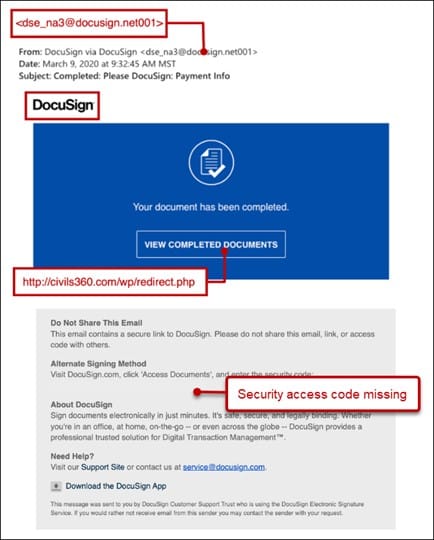
The email attempts to imitate a secure document request from DocuSign, using phrases like “Review Documents,” “Access Documents,” and “Security Code.” It also includes standard-looking disclaimers about not sharing the email and instructions for alternate signing methods. On the surface, it resembles the types of communications repo companies deal with every day. In reality, it is not sent through DocuSign at all and does not originate from any legitimate document platform.
In plain terms, this is a trap. The message is crafted to make you believe a lender or recovery company has sent you a time-sensitive complaint or compliance document that requires your signature. If you click the link, you are not taken to DocuSign—you are redirected to a fraudulent website designed to look like it. From there, the goal is simple: capture your login credentials. Once entered, your email account and potentially your business systems can be compromised.
From a technical standpoint, the email fails multiple authenticity checks despite appearing legitimate to the average user. The message originates from a free webmail account rather than an authorized sending domain. While it references DocuSign, there is no evidence of transmission through DocuSign’s infrastructure. The links embedded in the email resolve to non-DocuSign domains, including unrelated hosting services commonly used in phishing campaigns. This mismatch between displayed branding and actual link destination is a primary indicator of credential harvesting attempts.
Additionally, the message uses social engineering techniques tailored to the repossession industry. The inclusion of terms like “pickup,” “complaint handling,” and references to major lenders is intentional. These elements are meant to create urgency and legitimacy, increasing the likelihood that the recipient will act without verifying the source. The structured formatting, signature request language, and security code are all copied from legitimate templates, but the delivery mechanism is entirely fraudulent.
It’s also worth noting that the email passed certain basic authentication checks, such as DKIM signing from a legitimate email provider. This does not make it safe. Attackers often rely on trusted platforms like Yahoo or Gmail to send phishing emails specifically because they can pass these checks while still being malicious. In this case, SPF alignment was neutral, and the sending infrastructure included third-party relay services—another red flag when combined with impersonation of a trusted brand.
For repo agencies, the risk here is significant. If a user enters their credentials into a fake login page, attackers can gain access to internal communications, client data, assignment details, and forwarding systems. From there, the attack can spread laterally—sending additional phishing emails from compromised accounts, making detection even more difficult.
The safest approach is simple but critical. Any email requesting a document signature—especially one tied to complaints or lender notifications—should be verified before clicking anything. Legitimate DocuSign emails will come from official domains and can be accessed directly by logging into your DocuSign account, not through embedded links. If there’s any doubt, contact the supposed sender through a known, trusted method—not the email itself.
This campaign is not random spam. It is targeted, industry-specific, and designed to exploit the exact workflows repossession companies rely on every day. Agencies should alert their staff immediately, reinforce link verification practices, and treat any unexpected “signature request” tied to a repo file or complaint as suspicious until proven otherwise.
Dave Branch